Protect Your Business with Our Advanced
Cyber Security Service
Protecting Your Digital World With Our Cyber Security Service
In today’s digital world, cyber threats are evolving rapidly, putting businesses of all sizes at risk of data breaches, malware, and unauthorized access. A single security lapse can lead to financial loss and reputational damage.
At Gulf Origin, we deliver comprehensive cybersecurity solutions to keep your business secure. From threat detection and data encryption to compliance and security training, we ensure your digital assets stay protected.
With 24/7 expert security teams, we proactively identify vulnerabilities, neutralize threats, and safeguard your IT infrastructure so you can focus on growing your business worry-free.
/01
Aramco Cybersecurity Certification (SACS-002)
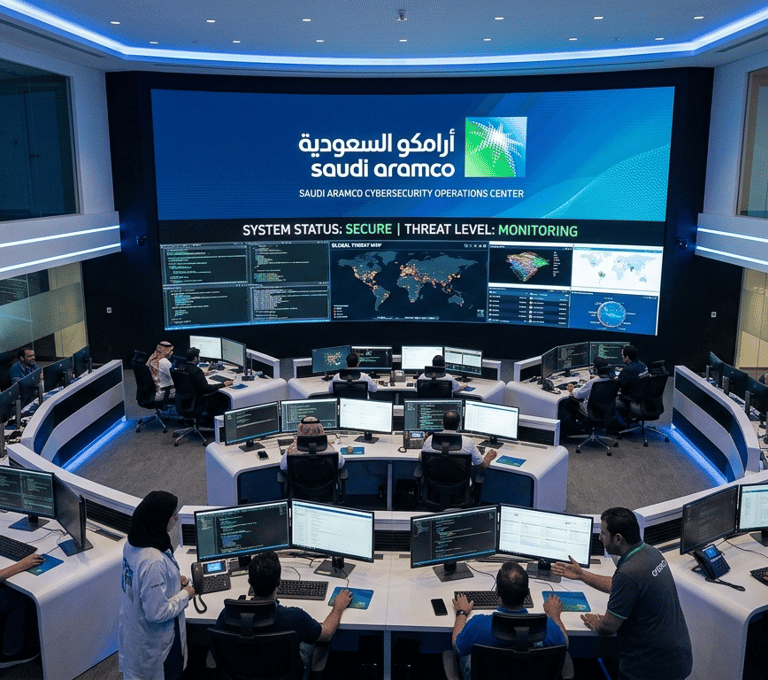

Aramco CCC Compliance – Why It Is Important and How We Help
The Cybersecurity Compliance Certificate (CCC) required by Saudi Aramco is a mandatory cybersecurity certification for vendors and contractors who want to work with Aramco or connect to its systems. This requirement exists to protect critical oil and gas infrastructure from cyber threats and to ensure that every organization within Aramco’s supply chain follows strong cybersecurity practices.
Without CCC certification, companies may face delays in project onboarding, restricted system access, or may be unable to work with Aramco at all. Achieving CCC compliance demonstrates that an organization has implemented essential security controls such as secure access management, network protection, vulnerability management, and proper cybersecurity governance.
Our company simplifies the entire CCC compliance process so organizations can focus on their core business while we handle the technical and compliance work. Our team performs a complete gap assessment to identify security areas that need improvement. We then support the implementation of required cybersecurity controls, prepare all necessary policies and documentation, and ensure your environment meets CCC requirements.
We also prepare the final compliance report and guide your organization through the audit process, assisting during audit sessions to ensure everything runs smoothly. With our expertise managing the implementation, documentation, and compliance preparation, you can stay confident and relaxed while we handle the complex steps required to achieve CCC certification.
/02
SABIC Cyber Trust Program Compliance


SABIC Cybertrust Compliance – Why It Matters and How We Support You
Companies working with SABIC must comply with the Cybertrust cybersecurity framework to ensure that vendors maintain strong security practices when interacting with SABIC systems and infrastructure. Cybertrust compliance helps protect SABIC’s digital environment from cyber risks that could originate from third-party vendors.
For organizations that want to collaborate with SABIC, meeting Cybertrust requirements is essential. It demonstrates that the company has implemented secure systems, controlled user access, and maintains proper cybersecurity monitoring and policies.
Our company helps organizations achieve Cybertrust compliance through a structured and efficient process. We begin with a cybersecurity gap assessment to evaluate your current environment against Cybertrust requirements. Based on this assessment, we assist with implementing the required security controls and preparing the necessary documentation and policies.
Our team also prepares the final compliance report and supports your organization throughout the review and audit process. From implementation to documentation and audit assistance, we manage the entire compliance journey so you can remain focused on your business while we ensure your organization meets SABIC Cybertrust requirements successfully.
/02
Advanced Threat Detection & Response


Stay One Step Ahead of Cyber Threats
In today’s digital age, cyber threats are constantly evolving. Our advanced threat detection and response solutions protect your systems against malware, ransomware, and unauthorized access.
Key Benefits:-
Real-time threat monitoring to detect cyberattacks instantly.
Automated incident response to minimize downtime.
AI-driven security analytics for proactive threat prevention.
24/7 security operations center (SOC) for continuous protection.


/03
VULNERABILITY ASSESSMENT & PENETRATION TESTING
Identify Risks Before Hackers Do
Vulnerability Assessment & Penetration Testing (VAPT) services are designed to proactively uncover security gaps in your applications, networks, and systems. With real-world attack simulations and in-depth assessments, we help you strengthen your digital infrastructure and ensure compliance—before threats turn into breaches.
Key Features :-
Web Application Penetration Testing
Mobile Application Penetration Testing
API Security Testing
Thick Client Application Testing
Network Penetration Testing
Network Segmentation Testing
Source Code Analysis
One-Time Password (OTP) Functionality Testing
Breach and Attack Simulations
TLS Insecurity Identification
WiFi Penetration Testing
/04
Endpoint Protection & Network Security


Secure Every Device & Your Entire Network
Your business is only as secure as its weakest link. Our endpoint protection and network security solutions provide multi-layered defense to safeguard your IT infrastructure.
Key Features:-
Next-gen firewall for strong perimeter security.
AI-powered antivirus to block malicious software.
Zero Trust security model to prevent unauthorized access.
Secure remote access (VPN & MFA) for work-from-anywhere safety.


/05
Data Privacy & Encryption Services
Keep Your Sensitive Data Safe & Confidential
Data breaches can be devastating. Our data privacy and encryption solutions ensure your sensitive information remains secure at rest, in transit, or in use.
How We Protect Your Data: :-
End-to-end encryption for emails, files, and transactions
Data loss prevention (DLP) to stop unauthorized sharing
Cloud security solutions for SaaS and hybrid environments
Regulatory compliance support (GDPR, HIPAA, ISO 27001, etc.)
/06
Security Awareness Training & Compliance


Educate, Empower & Strengthen Your Cyber Defenses
90% of cyberattacks happen due to human error. Our security awareness training ensures that your employees recognize threats and follow best practices to prevent attacks.
What We Offer :
Phishing simulation tests to educate employees.
Interactive cybersecurity training modules.
Compliance & regulatory guidance for industry standards.
Custom security policies & best practices for your organization.
Why Choose us
Expert-Led Security
Solutions
Trusted by businesses worldwide
AI-driven monitoring & response
Meets global security standards
Proactive Cyber
Defense
Compliance-Ready
Security
Customized
Protection
Tailored to your business needs
Contact us for a cybersecurity assessment.
Secure your business
today!

Building strong alliances with global leaders in technology and innovation!







Our Trusted Partners
// Let’s Build the Future Together
Get in touch today to take your business to the next level!


About Us
+966 531481024
Copyright © 2025 Gulf Origin. All Rights Reserved.
Gulf Origin Solutions – Leading IT & cybersecurity experts in Riyadh, driving digital transformation and security for businesses, government, and critical infrastructure in line with Vision 2030.
Our Services
Other Links
Contact Us
Follow Us On
IT Intrastructure
Digital Transformation
Compliance & Risk Management
Blogs
Info@gulforigintech.com
Riyadh,Saudi Arabia
